Trust Issues #12: American bank First National Bank of Omaha uses odd login domain

First National Bank of Omaha is a major US bank. Their holding company, First National of Nebraska, has nearly 5,000 employees and $26 billion in assets.
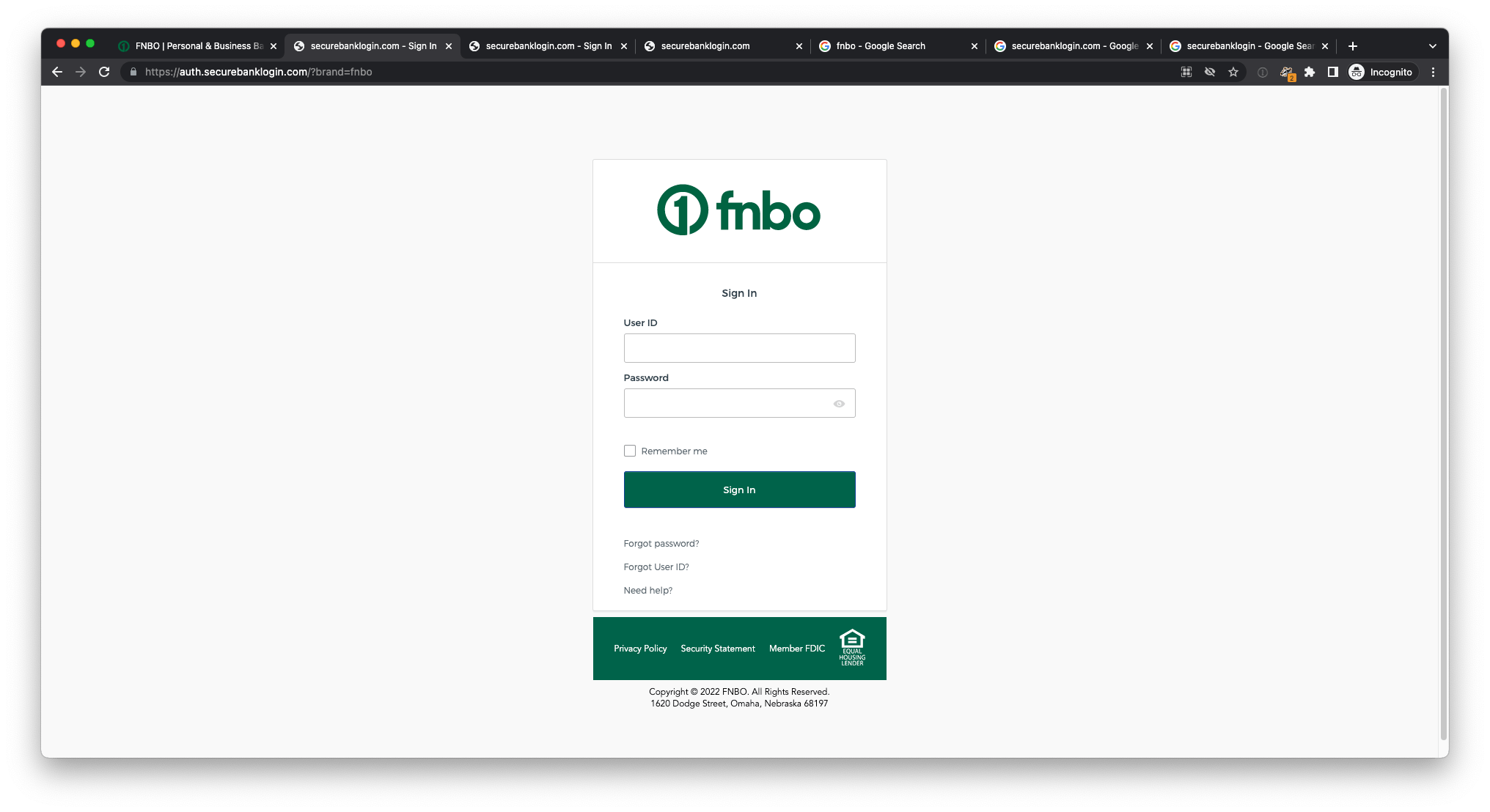
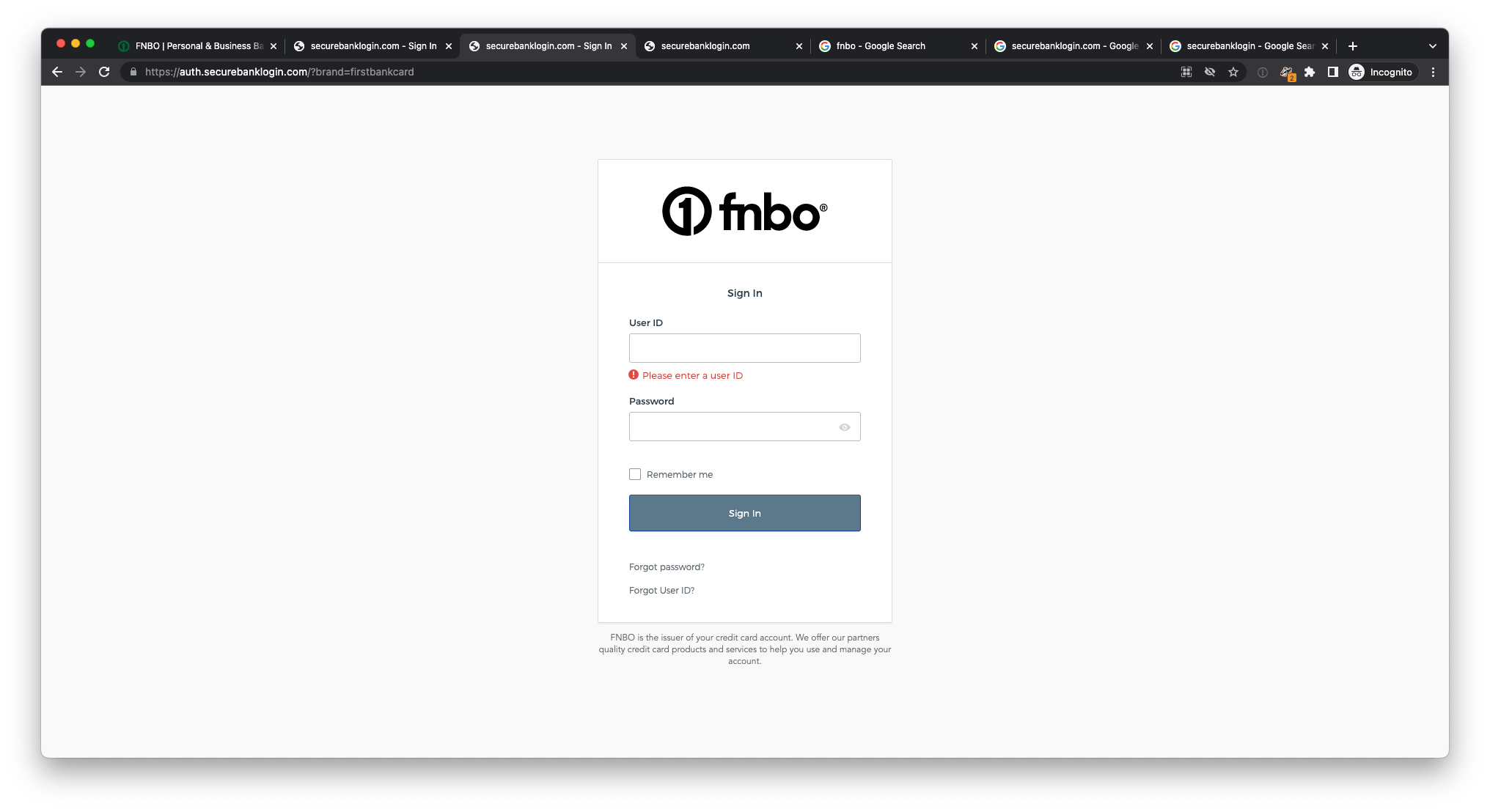
FNBO’s main domain is "fnbo·com". When logging in, you are taken to a site on a different domain — "auth·securebanklogin·com/?brand=fnbo".
The nature of the domain "securebanklogin·com" feeds into the ignorant and outdated cyber security narrative — the era of ‘if you see a padlock it’s secure’ and ‘if you see “https” it’s secure’. This outmoded attitude says HTTPS means security, but HTTPS and a padlock merely confer encryption to a server, not which server (not the one you necessarily intend). In a similar defunct vein, the domain says “secure” in it, so some would say it must be secure right? Except, anyone can register a domain name and put “secure” in it. Saying “secure” doesn’t make it so.
The domain, so generic, doesn’t have the bank name in it. It is so vague that it would fit in with a phishing campaign that targets a range of banks. Normally, phishing campaigns are forced to become more sophisticated over time as defences and awareness improve, but with this domain being so phishy in appearance, malicious actors can exploit customers’ trust and register traditionally phishy looking domains and be accepted by users unwittingly.
It was once common, until around five years ago, for banks to host login on a different domain to their main site, because encryption across your whole domain was difficult and expensive, with SSL/TLS certificates also costly. Securing your main domain with vast numbers of disparate pages and providers was a tall order, especially when most of it was for information and marketing purposes, so you kept most of your pages on HTTP. Now, HTTPS encryption is widespread and expected by users, and most banks host login on their primary domain, for trust reasons.
FNBO uses "securebanklogin·com" as a central auth domain for all their bank service logins, like their customer bank and credit card services. But they should use a central domain which has their name in it for better trust.
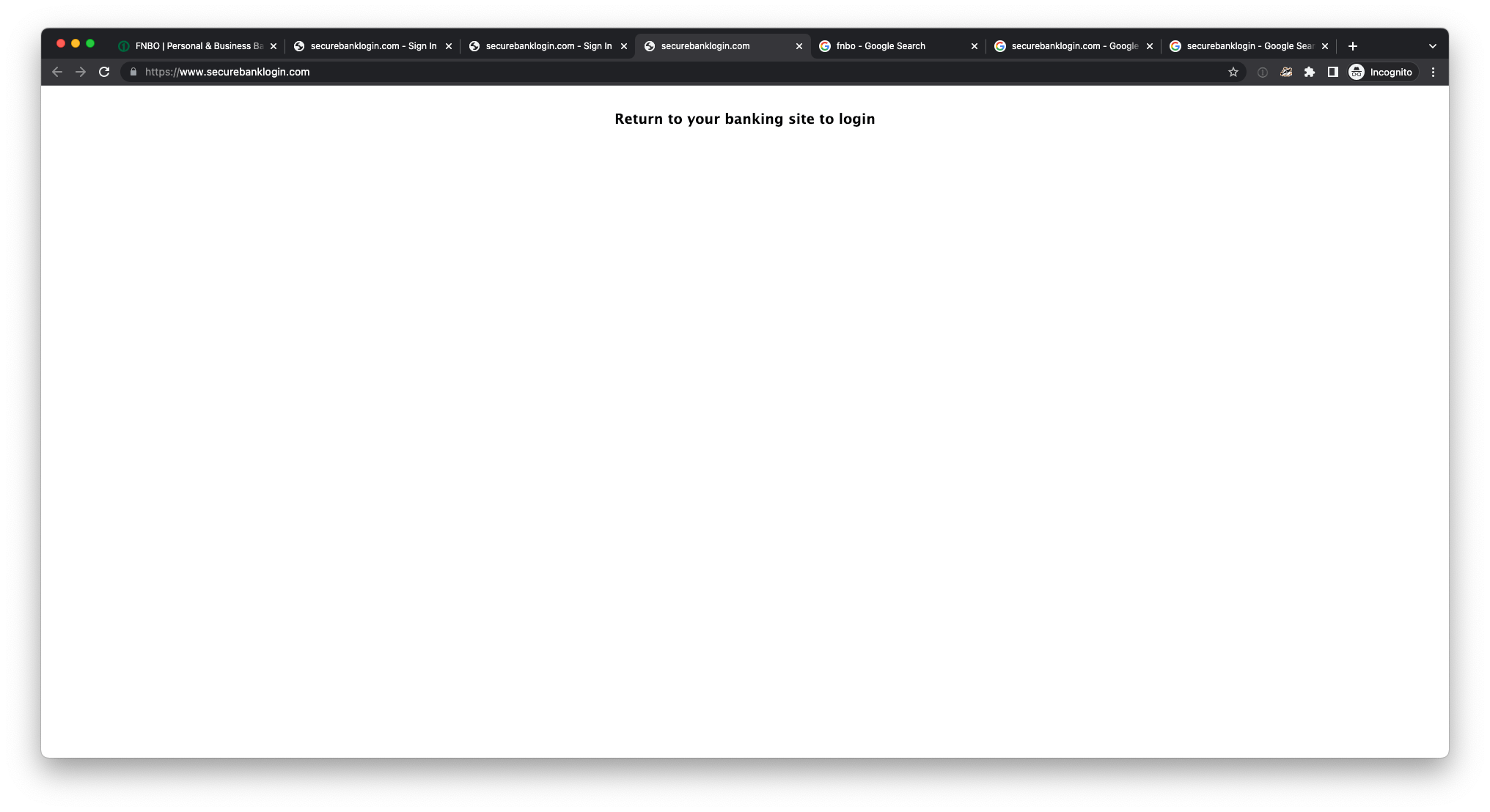
When you visit the root domain "securebanklogin·com" without the specific bank to log in to, it just says “return to your banking site to login”. There is no branding here, no indication this is FNBO. With such a sparse page, it is strikingly similar to the way some phishing sites return a blank or innocuous page when you visit anything but the target page, to try and hide their nature to systems and people.
When FNBO registered "securebanklogin·com", it appears first registered in 2005, and with current registration dated 2015, they must have thought our users won’t understand it’s secure unless we say it in the domain, and might have been so expansionist that they thought they would be running all sorts of banks in the future, not just those under the First National umbrella.
It’s possible that FNBO took ownership of "securebanklogin·com" after misuse by phishing actors, but in this case the domain should be controlled, not in active use, and not used as their main login domain.
Phishing actors frequently add the words “login” and “secure” to brand names in malicious domains that they create and control. Many brands don’t register domains with extra words in various combinations, and it’s not reasonable to capture all malicious possibilities. With this domain, "securebanklogin·com", a rearrangement of the words “secure bank login” could be registered for malicious purposes. For example, "secureloginbank·com" and "banksecurelogin·com" are both completely different of course, but would fool many people — they scan in such a similar way. Threat actors would find this generic domain easier to create alternative malicious domains for, using similar generic words from a vast set, compared to brand-centric domains.
This domain, "securebanklogin·com", makes us question our judgement. It’s official but doesn’t look so. In order to log in, we have to suspend our normal trust reasoning and try to remember this domain for the bank. But in all likelihood, it degrades the cognitive signals we use to determine trust and safety for domains we see in the future. Bad sites will get through the phishing net more easily.
The issues highlighted will pass many users by. Many will click and follow links they receive without much inspection. Technology and security are so complex today and change so quickly that they expect systems will deal with cyber issues, and that it’s not their concern. Sadly, it is still mostly the user’s concern.